ISLAMABAD – Networking social giant LinkedIn comes under new scrutiny as Fairlinked e.V. raised serious privacy concerns about LinkedIn, alleging platform may quietly scan users’ browsers for installed extensions without their knowledge.
The discovery, part of the BrowserGate campaign, suggests scans occur automatically when LinkedIn loads on browsers like Google Chrome and Microsoft Edge. Because LinkedIn profiles are tied to real identities and workplaces, researchers warn the detected tools could reveal sensitive insights about users’ behavior and the technologies used within their organizations.
A major privacy controversy is erupting around LinkedIn after investigators alleged the professional networking platform may be secretly scanning users’ web browsers to identify installed software, without their knowledge or consent.
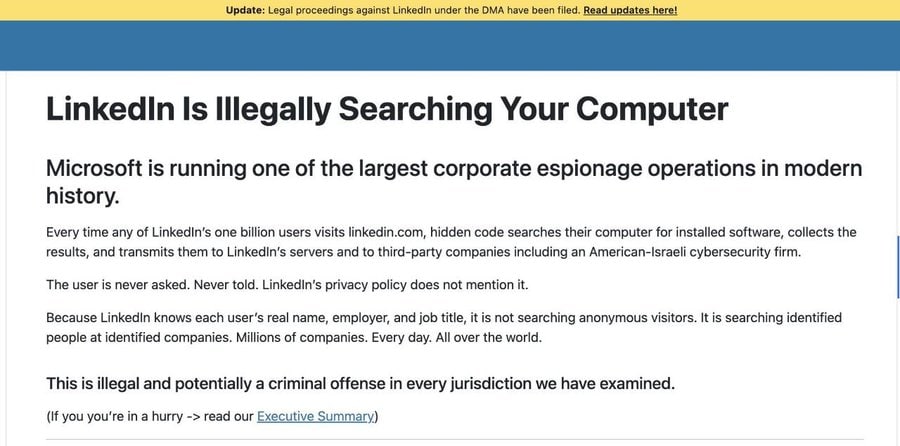
The allegations come from new investigation by European digital rights organization Fairlinked e.V., carried out under a campaign called “BrowserGate.” According to the group, LinkedIn allegedly runs hidden JavaScript code that quietly checks users’ browsers for thousands of installed extensions whenever the website loads.
Researchers claim the scanning occurs automatically on Chromium-based browsers including Google Chrome, Microsoft Edge, Brave, Opera, Vivaldi, and Arc. However, the investigation says the activity does not affect users of Mozilla Firefox or Apple Safari.
The script reportedly runs silently in the background and attempts to access publicly available files associated with browser extensions. By doing so, LinkedIn’s systems can determine whether specific add-ons are installed on a user’s browser. Investigators say the process completes within milliseconds and produces no visible warning or notification for users.
Perhaps most alarming is the scale of the scanning system. According to the investigation, LinkedIn’s internal code references more than 6,000 browser extension identifiers. This means the platform could potentially detect thousands of different tools installed on a user’s device.
Because LinkedIn profiles are tied to real-world identities, employment histories, and workplaces, every detected extension could theoretically be linked directly to an identifiable individual. Investigators warn this could allow LinkedIn to infer personal behavior patterns, workplace technologies, and even the digital infrastructure used by entire organizations.
The investigation also highlights types of extensions that could be detected. These reportedly include hundreds connected to job-hunting platforms, potentially exposing professionals who are secretly searching for new employment while maintaining active LinkedIn profiles. Other detectable extensions are said to include tools associated with religious communities, political news sources, accessibility software, neurodivergent support tools, and even competing sales or business platforms.
It was found that LinkedIn pages may load additional hidden tracking components, including scripts connected to cybersecurity firm HUMAN Security, along with background processes tied to Google services. Investigators claim these elements operate invisibly, placing tracking cookies and transmitting encrypted data during normal browsing sessions.
LinkedIn has yet to respond to these allegations at the time of reporting. However, if the findings are verified, the case could escalate into one of the most significant corporate privacy investigations involving a global social media platform.
WhatsApp Hack Alert: Your messages might already be compromised